iscsiadm Command Connect & Manage iSCSI – RHEL 7/Centos 7
The iscsiadm utility is a command-line tool allowing discovery and login to iSCSI targets, as well as access and management of the open-iscsi database. iscsiadm command is used to connect and manage iSCSI LUN’s/Disks from SAN storage. Default iscsi port number is 3260, if you specify another port number while configuring iscsi server then use that particular number while iscsi login logout and discovery.
Open-iscsi does not use the term node as defined by the iSCSI RFC, where a node is a single iSCSI initiator or target. Open-iscsi uses the term node to refer to a portal on a target.
For session mode, a session id (sid) is used. The sid of a session can be found by running iscsiadm -m session -P 1. The session id and sysfs path are not currently persistent and is partially determined by when the session is setup.
Note that many of the node and discovery operations require that the iSCSI daemon (iscsid) be running.
iscsiadm command to manage iSCSI disks in RHEL 7
# yum install iscsi-initiator-utils
after installation of required packages you need to verify iscsi daemon services, using below command
systemctl status iscsi.service
You must be run iscsiadm command as root/super user are else it through below error
Arkit:~]$ iscsiadm --mode discoverydb --type sendtargets --portal 192.168.2.62 --discover iscsiadm: Maybe you are not root? iscsiadm: Could not lock discovery DB: /var/lock/iscsi/lock.write: Permission denied
Discover targets by querying SAN IP address
below iscsiadm command will discover the mapped LUN’s/Disks from SAN IP address which are ready to use.
[root@TechArkit:~]# iscsiadm --mode discoverydb --type sendtargets --portal 192.168.2.62 --discover
iscsiadm -m discoverydb -t st -p ip:port -I iface0 -I iface2 --discover
You also use above command to specify the multiple interfaces while running discovery query iscsi.
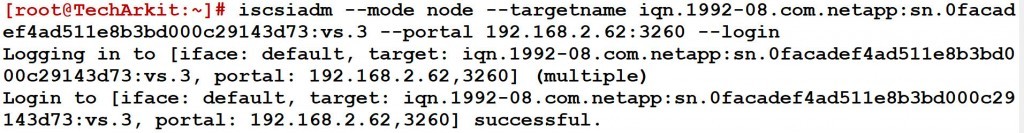
Login target using iscsiadm command
Let’s note discovery output and take the target name from it. Using target-name of remote SAN device to login the iscsi disk (Which means establish the iscsi connection)
iscsiadm --mode node --targetname iqn.1992-08.com.netapp:sn.0facadef4ad511e8b3bd000c29143d73:vs.3 --portal 192.168.2.62:3260 --login
iscsiadm -m node -T targetname -p ipaddress -l /sbin/iscsiadm -m node --loginall=automatic
Using automatic loginall parameters simply login all the targets with specifying particular target name
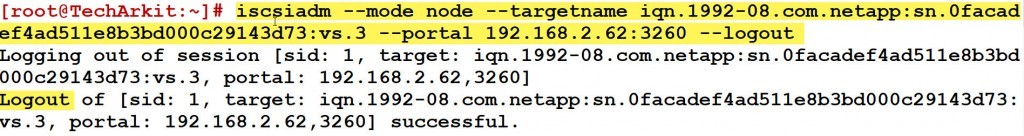
Logout target using iscsiadm command
you can logout the login target-name using below command, which will disconnect the iscsi disk from portal
iscsiadm –mode node –targetname iqn.1992-08.com.netapp:sn.0facadead511e8b3bd000c29143d73:vs.3 –portal 192.168.2.62:3260 –logout
iscsiadm -m node -T targetname -p ipaddress -u /sbin/iscsiadm -m node --logoutall=all
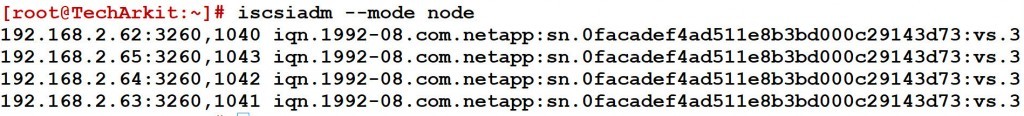
Display node records
simply list node records using iscsi mode as node
iscsiadm --mode node
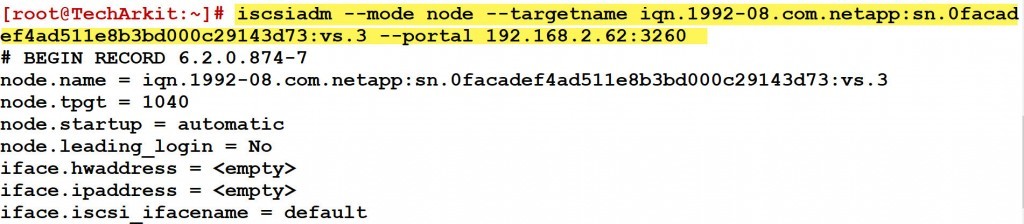
List detailed information about node
which iscsiadm command provides detailed information about node, including iscsi parameters
iscsiadm --mode node --targetname iqn.1992-08.com.netapp:sn.0adef4ad511e8b3bd000c29143d73:vs.3 --portal 192.168.2.62:3260
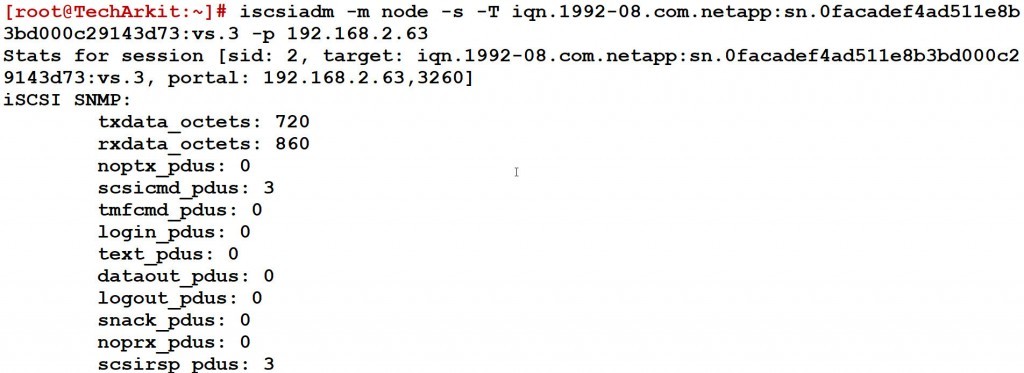
Display Login session Statistics
This command only works when you have logged in sessions, if there is no iscsi logged in sessions it displays that no session currently
iscsiadm -m node -s -T TargetName -p 192.168.2.63
Find iscsi Logged in Sessions
iscsiadm -m session
Related Articles
iscsi server installation and configuration step by step guide RHEL 7
SAN Boot Setup using iscsi LUN
Could not create NetworkPortal in config
Thanks for Your Wonderful Support and Encouragement
More than 40,000 techies are part of our ARKIT community. Join us today and keep learning Linux, Cloud, Storage, DevOps, and IT technologies.








one more command i need to add this article if session are already login so unable to see the the HD so run this command # iscsiadm -m session –rescan
Thanks